We have been using Intel SATA SSDs in server settings for a very long time now. We have yet to hit one server, all virtualization platforms, exhaust any of the SSDs we’ve deployed. We’ve also been deploying HGST SAS SSDs in production for a very long time now. Same story, […]
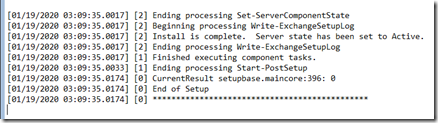
We are installing Exchange 2019 CU4 into Server Core 2019 for the first time in a greenfield setting. We a strange snag that turned up very little in the way of search results on the error. The organization name, First,Organization, can’t be used because it contains invalid characters. The setup […]
As the subject says, there is basically an open door in the way RD Gateway handles incoming packets. Whether it is being exploited in the wild as of this writing is questionable. That being said, this is a bad one folks. Get those RD Gateway servers patched up. Oh, and […]
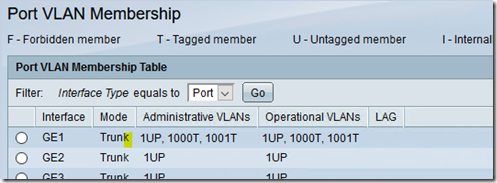
We have a pair of Cisco SG500x switches that we are setting up in a redundant configuration, so not stacked, that require a number of VLANs to be configured. VLAN 1: Default Untagged VLAN 1000: Tagged VLAN 1001: Tagged VLAN 1002: Tagged ETC Depending on the device connected to the […]
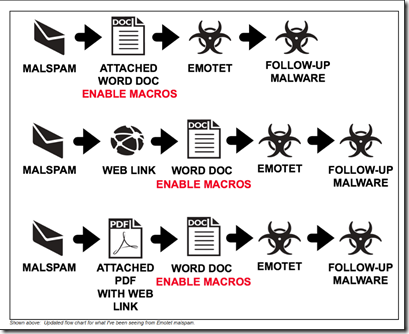
The following is a list of things we can do to help protect our client’s networks from a Ransomware Attack or recover from one if someone does end up doing something they should not have. Train users to not click ENABLE MACROs. Image Credit: https://www.malware-traffic-analysis.net Remember, those little EXTERNAL flags […]
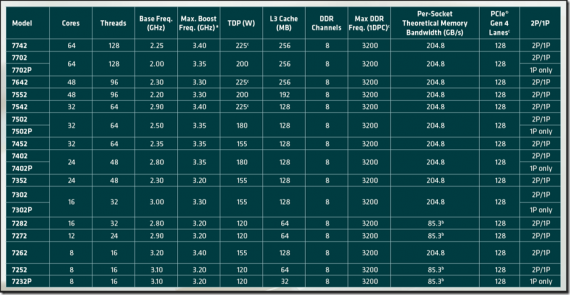
Courtesy of AMD (thanks Marco!), we have a couple AMD EPYC Rome 7502 series CPUs for our systems we plan on Azure Stack HCI certifying! AMD EPYC Rome 7502 Processors with Intel Scalable Socket Cover In the above image we laid an Intel Xeon Scalable socket cover above the AMD […]
We’ve updated our slipstream guide. A link to the OSCDImg download via the ADK is now included along with some additional instructions. Crayon has been loaded and tweaked to work with our WordPress so the script is so much easier to read. 🙂 OS Guide: Slipstream Updates Using DISM and […]
This news is more than disappointing: Personal and Social information of 1.2 billion people Discovered in Massive Data Leak The old cliché: Ignorance is Bliss Anyone else out there not know what “Data Enrichment” is and that there are companies out there that do this and then sell that information? […]
We’ve been running Haier commercial dual hose 13K BTU portable air conditioners for a long time now. The model we were using went through a design “refresh” within the last year. The “new” model has had pretty much a 100% fail rate. In a few locations where a single hose […]
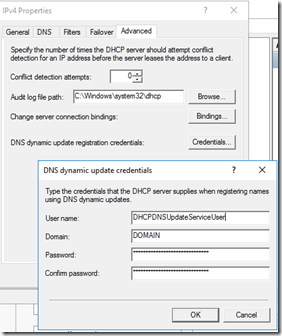
The following comment was made on a mailing list we are a part of: We keep 8.8.8.8 as a secondary DNS server in DHCP in case the primary DNS server goes offline. No. Bad Practice. Period. Never, ever, put a public DNS server IP address as a frame of reference […]