We just completed a workstation board swap of an ASRock TRX40 Creator board that was set up with an Asus HYPER M.2 x16 Card (link to current product). We had plugged everything back in and hit the power button on the board for that first boot then jumped up to […]
How-To
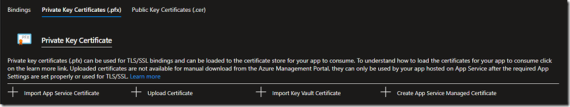
We use IIS to create the CSR and to complete the Certificate Request. We use the Computer Certificates MMC to export that certificate to .PFX. When exporting with the intent to import the .PFX into Azure we run the following steps: Open the Computer Certificates MMC Click on Start and […]
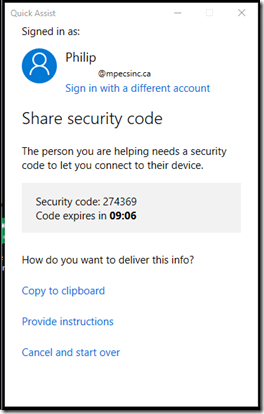
With the demise of the CoPilot service we’ve been using for about a decade now, we had to look for something to replace it. CoPilot was a simple to use remote desktop shadowing product that was very reasonable in cost. What we’ve come to use is free and built-in to […]
The following is a recipe that we’d look at using for a backup destination for Veeam. Our current preference is for Storage Spaces set up for the requested 64KB Allocation Size but we’re looking into Linux Harden Repositories as an option. FreeNAS Operating System Ubuntu Server Distro Silverstone CS381 Chassis […]
We’ve added the following PowerShell Guide to our KB: PowerShell Guide: Install Exchange 2019 CU11+ into Windows Server Core The above PowerShell allows us to install on Windows Server Core but it also has the setup for breaking out the three components of Exchange into their own partition: D: Exchange […]
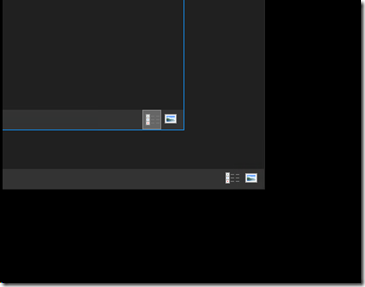
One of the annoyances when working with multiple windows open is the inability to see their edges out of the box. A simple remedy: Start Settings Colors Choose an accent color Tick Start, taskbar, and action center Tick Title bars and window borders For those of us who are visually […]
There are many ways one can go about setting up the networking for an Azure Stack HCI (ASHCI)/Storage Spaces Direct (S2D) hyper-converged infrastructure (HCI) cluster. TL;DR Our rule of thumb is to start with four 25GbE ports via two network adapters for multiple nodes requiring switches or even in smaller […]
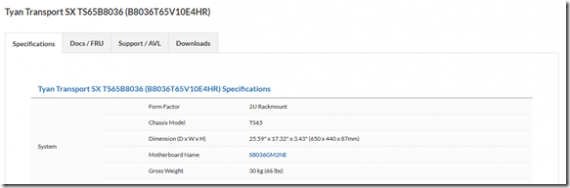
TYAN has an excellent built-in Remote Management Module (RMM) that does not require an extra license like some Tier 1 vendors do. TYAN Default Administrator Username and Password The default TYAN username and password is: Username: root Password: superuser The first thing we do when we sign in is create […]
We took some time today to add the following PowerShell Guide to our repository: New-VM Template: Gen2 SecureBoot Linux We ran into a snag installing the latest Ubuntu Server software with the .ISO refusing to boot unless we turned SecureBoot off. As it turns out, thanks to a pointer from […]
After an evaluation of the various cloud storage vendors and their cost to store our backups there we decided on the following: Veeam Backup & Replication v10 StarWind Virtual Tape Library (VTL) BackBlaze B2 At the bottom of the B2 link is a calculator showing the savings over the others. […]